Alternatives: In-House or Outsource?
If you are close to meeting the requirements of an HHS OCR audit, or if you have a savvy team, it might make sense to implement HIPAA-compliant elements in-house — with a checkoff from a third-party auditor. While this approach provides greater control over the elements required for compliance, it also requires a greater investment in internal resources and expertise.
It is important to note that individual auditors do not use one single standard. Each auditor interprets the HIPAA controls in their own way and has an unique assessment process. The danger of insourcing all HIPAA work is there may be a huge gap between your internal staff’s interpretation of the HIPAA policies and how an auditor interprets those same rules. Down the line, this could result in costly rework to address deficiencies found by your auditors.
There are two approaches to combat this issue. The first and more expensive, but thorough, option is to have the auditor perform a quick pre-assessment. This allows the auditor to get a quick view of the landscape and provide directional feedback regarding major gaps. A second, cheaper approach is to ask the auditor to provide documentation and guidance on how to adequately perform a self-assessment. With this, you can focus your work on areas that the auditors have deemed important and, hopefully, reduce the amount of deficiencies they find in a full audit.
If internal compliance work is too burdensome, you may consider outsourcing PHI management to a reputable HIPAA-compliant vendor who in turn acts as a BA (and yes, BAs can subcontract to other BAs!). This option would be especially attractive for an organization that is sub-scale in size, where a direct investment in HIPAA expertise would be disproportionately large. Fortunately, a number of established vendors now offer platforms that meet HIPAA requirements and are willing to sign the BA agreement, including Amazon Web Services, Datapipe, and OnRamp.
Regardless of the approach you pick, it is crucial to document everything — discussions, policies, procedures, trainings. This “paper trail” will be central to any future audit, whether self-imposed or by HHS. Detailed documentation will be especially important as your team grows, ensuring that all members of your organization are aware of HIPAA rules and how they apply to each role. If you take all the necessary steps for HIPAA compliance yet fail to keep proper records, the resources you invested may be all for naught.
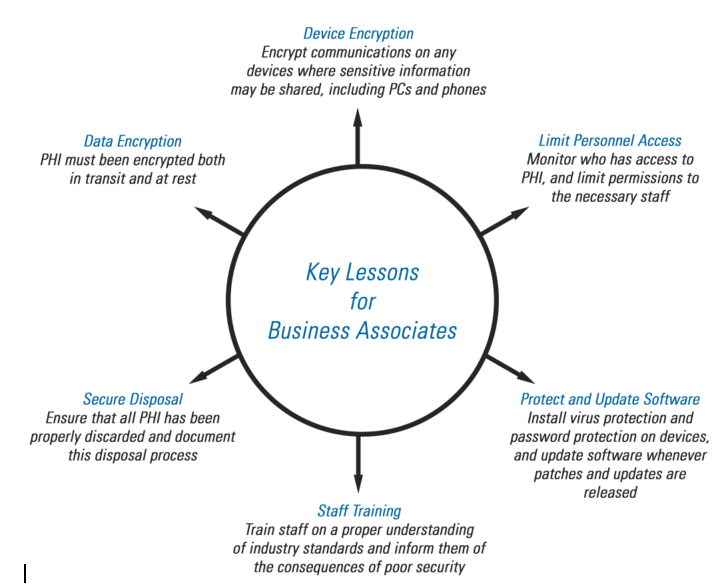
Key Lessons from HIPAA Compliance Initiatives
Our experience with numerous healthcare-focused companies has given us great perspective on how to best deal with HIPAA-related challenges. For example, a web company that provides healthy meal planning services processes biometric data to determine consumer health profiles. They can detect conditions like diabetes, obesity, and high blood pressure, then tailor meal plans for healthier outcomes. Being a startup, the company did not have a lot of resources to spend on compliance. A crucial strategy for them was to take as much of the system out of scope as possible.
The company’s system was made up of two major components: the customer facing website, and a large data warehouse used to run machine learning algorithms to make recommendations. To minimize the audit’s scope, they made sure the data warehouse never contained any biometric data. Instead, they performed a pre-processing routine that populated various attributes in the data warehouse based on the biometrics.
To meet HIPAA requirements, biometric data must be encrypted in flight and at rest in databases or file servers. However, encryption creates performance overhead, a critical issue for a consumer-facing web application. In order to minimize the impact of encryption, the company isolated all of the biometric data to a single table and encrypted only that table. They used table-level encryption, as opposed to attribute-level encryption, to protect against unencrypted addition of future attributes. This way, the biometrics table is used once, when the customer first logs in, while the rest of the tables are unencrypted and contain no sensitive data — allowing for maximum performance while still protecting PHI.
Per HIPAA requirements, the web company also had to retool their approach to people and processes. For example, they were required to show proof of destruction of the original biometrics sent to them from their clients. The company’s customers were large employers who offered the website to employees as a human resources perk, providing health advice and lowering insurance premiums in exchange for using their biometric data.
For employees who opted into the service, the employer sent their biometric data via file transfer or email to the web company. To succeed in a HIPAA audit, the web company strictly limited personnel access to these files and developed a documented process for destroying the original data source after it was ingested.
In addition, areas as simple as PC and phone encryption could not be overlooked. Imagine that an employee receives a file containing biometric data from a customer and the employee’s laptop or mobile phone becomes compromised — the biometrics file could easily wind up the wrong hands. In another example, a phone by the front desk was flagged by an auditor who noted that the IP phone could create a backdoor into the company’s network. The fix? We had to replace that phone with an old-school phone, without connectivity capabilities.
As evidenced by these anecdotes, HIPAA requirements will impact various teams and operations within your organization. While achieving compliance may seem daunting, keep in mind that a data breach would be even more costly — a strong motivator for tackling security and privacy issues sooner rather than later.
